42 aws best practices
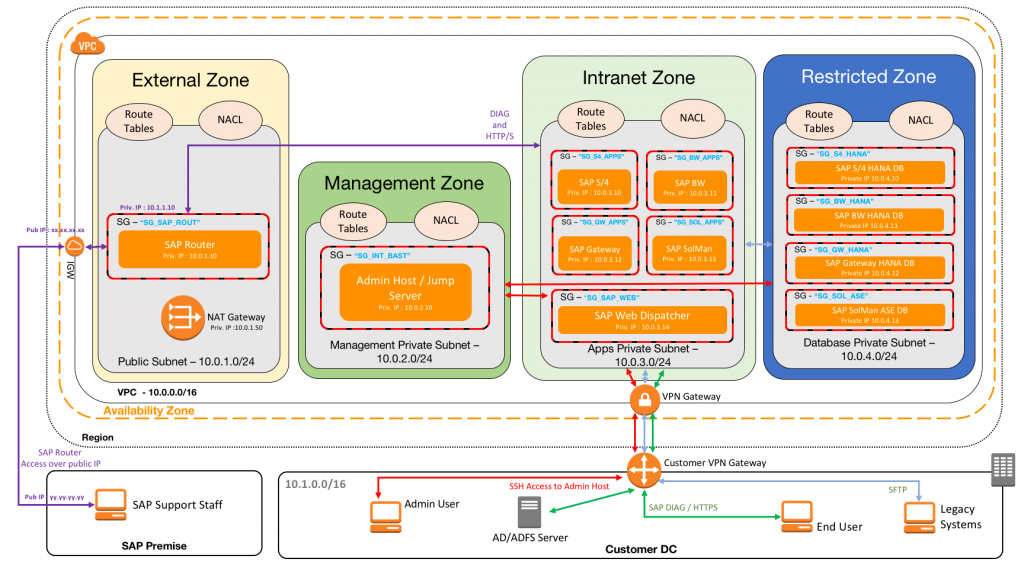
51 AWS Security Best Practices | McAfee Blog Below are some best practices around AWS database and data storage security: Ensure that no S3 Buckets are publicly readable/writeable unless required by the business. Turn on Redshift audit logging in order to support auditing and post-incident forensic investigations for a given database. Encrypt data stored in EBS as an added layer of security. AWS Best Practices: 3-Tier Infrastructure | San Diego | stratus10 AWS allows you to achieve high availability by distributing your application across multiple Availability Zones. Each Availability Zone is a physical data center in a different geographic location. For this AWS best practices post we have chosen to split up our network across 3 availability zones. This gives us high availability and redundancy.
Best Practices for Terraform AWS Tags AWS tags are key-value labels you can assign to AWS resources. that give extra information about it. DEPT® Cloud Engineering practice recommends the following AWS tags best practices: Define an explicit ruleset for tag key naming and stick with it.Inconsistent tags keys such as "appid", "Application ID", and "App_ID" are frustrating to use.
Aws best practices
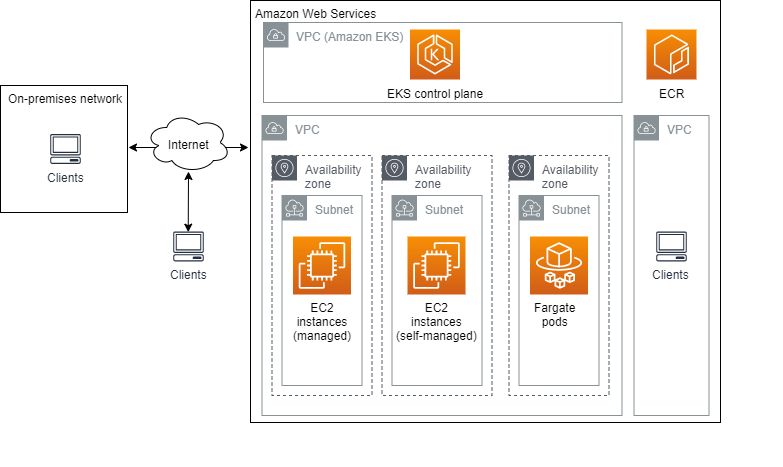
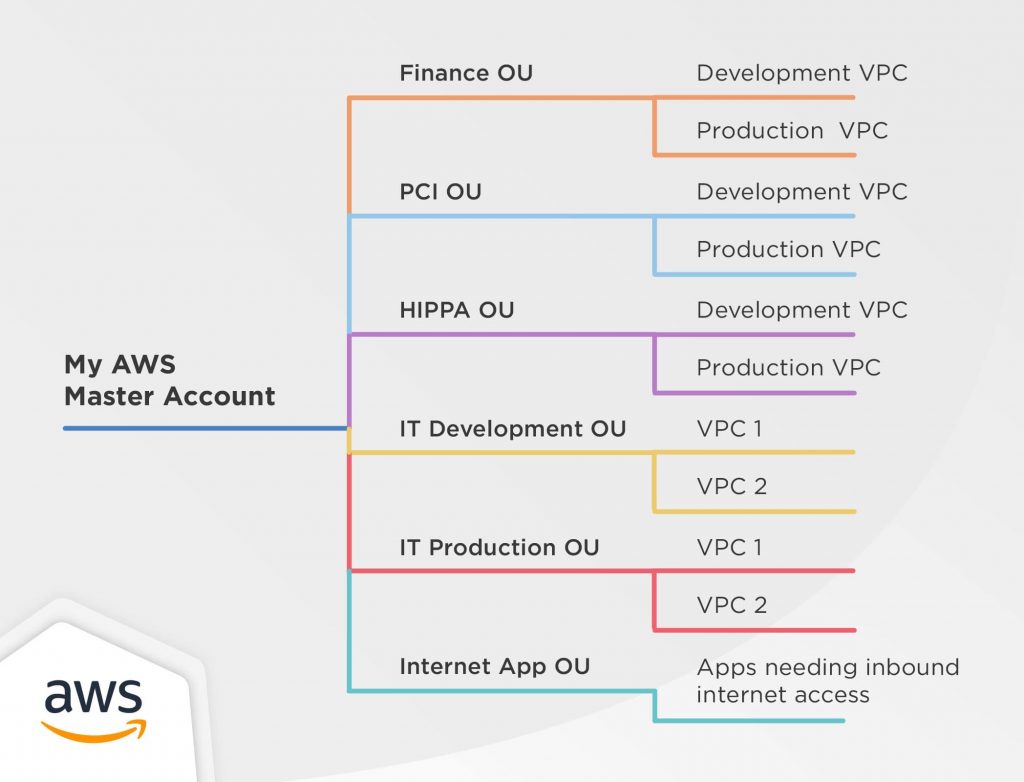
Establishing your best practice AWS environment Using a multi-account environment is an AWS best practice that offers several benefits: Rapid innovation with various requirements - You can allocate AWS accounts to different teams, projects, or products... Simplified billing - Using multiple AWS accounts simplifies how you allocate your AWS cost ... AWS Fargate Security Best Practices - Alert Logic AWS Fargate Security Best Practices. AWS has become one of the most popular options for running containers because of its high reliability, strong security, and native integrations. There are multiple ways to containerize applications on AWS depending on your needs. AWS Fargate is a highly turnkey solution that offloads infrastructure ... PDF Security Best Practices with Amazon ECR •ECR uses one AWS account for each stage: beta, gamma and prod •A micro-service has its own repoand deployment pipelinein each stage ... Best practices for ECR Image Scanning •Enable scan on push for each repository Turn on scan on push (it's free) for every repository. We're testing
Aws best practices. AWS best practices | Edge for Private Cloud v4.19.01 - Apigee Docs This section summarizes our best practices and provides our recommendations for using OPDK with AWS cloud. Cassandra is used as a backend and datastore for almost all the policies and is a critical part of the Apigee Edge runtime environment. This document focuses on optimizing Casssandra for the AWS environment. Storage and I/O requirements PDF Architecting for the loud Amazon Web Services - Architecting for the Cloud: AWS Best Practices Page 5 Design Principles The AWS Cloud includes many design patterns and architectural options that you can apply to a wide variety of use cases. Some key design principles of the AWS Cloud include scalability, disposable resources, automation, loose coupling managed services PDF AWS Key Management Service Best Practices - AWS Whitepaper AWS Key Management Service Best Practices AWS Whitepaper Introduction AWS Key Management Service (AWS KMS) is a managed service that makes it easy for you to create and control the encryption keys used to encrypt your data. AWS KMS uses Hardware Security Modules (HSMs) to protect the security of your keys. AWS Best Practices: five key approaches - Cloud Academy AWS Best Practices: Five Key Approaches to Get You Started 1. AWS Best Practices: protect your AWS credentials Your AWS account represents a business relationship between you and... 2. AWS Best Practices: secure your Applications Sometimes it is better to explain a concept with a picture or ...
VPC Best Practices | AWS: Security Best Practices on AWS - Packt A VPC can have a CIDR block ranging from /16 to /28, which means you can have between 65,536 and 16 IP addresses for your VPC. AWS recommends that you choose the highest CIDR block available, so always go for /16 CIDR block for your VPC. This way, you won't be short of IP addresses if you need to increase your instances exponentially. The 10 AWS Cost Optimization Best Practices - VMware Blogs The 10 AWS cost optimization best practices 1. Rightsizing EC2 Instances As we have already mentioned rightsizing, scheduling, and Reserved Instances/Savings Plans, let's start with these three AWS cost optimization best practices. The purpose of rightsizing is to match instance sizes to their workloads. 5 Best Practices for AWS NACLs (Network Access Control Lists) Play By the AWS NACL Rules While best practices help in avoiding errors or unwanted traffic, there are few NACL rules you must never ignore, such as: NACLs are always read in ascending order, with... PDF Amazon EMR Best Practices - d0.awsstatic.com Amazon Elastic MapReduce (EMR) is one such service that provides fully managed hosted Hadoop framework on top of Amazon Elastic Compute Cloud (EC2). In this paper, we highlight the best practices of moving data to AWS, collecting and aggregating the data, and discuss common architectural patterns for setting up and configuring Amazon EMR
Follow best practices | AWS Quick Starts - GitHub Pages If you're implementing Lambda-backed custom resources in your CloudFormation stack, review the best practices discussed in the AWS Support Knowledge Center. Linux Enable the -e flag at the top of all scripts (except user data) as follows: #!/bin/bash -e This will cause the script to exit with a non-zero exit code. 21 AWS Security Groups Best Practices | McAfee Blog As with any AWS service, it is crucial that AWS security groups are properly configured to protect against security risks and threats and best practices are followed: 1) VPC flow logging: Enable Virtual Private Cloud (VPC) flow logging. VPC flow logs provide visibility into network... 2) EC2: Ensure ... Getting Started: Follow Security Best Practices as You Configure Your ... Best practices to help secure your AWS resources Create a strong password for your AWS resources. To help ensure that you protect your AWS resources, first set a strong... Use a group email alias with your AWS account. If for any reason you are unavailable to respond to an AWS notification... Enable ... [AWS] Naming Conventions Best Practices · Carlos Requena A naming convention is a well-defined set of rules useful for choosing the name of an AWS resource. Ensure that your AWS resources are using appropriate naming conventions for tagging in order to manage them more efficiently and adhere to AWS resource tagging best practices. Naming (tagging) your AWS resources consistently have several ...
Welcome - Terraform Best Practices Welcome - Terraform Best Practices Welcome This document is an attempt to systematically describe best practices using Terraform and provide recommendations for the most frequent problems Terraform users experience.
Best practices to create & organize Terraform code for AWS The collaborative infrastructure-as-code workflow is built on multiple IT best practices (like using version control and preventing manual changes), and one must adopt the foundations before we can...
aws/aws-eks-best-practices - GitHub GitHub - aws/aws-eks-best-practices: A best practices guide for day 2 operations, including operational excellence, security, reliability, performance efficiency, and cost optimization. master 2 branches 0 tags Go to file Code jicowan Merge pull request #225 from sotoiwa/inspector-v2 78b47d4 7 days ago 980 commits .github Update main.yml
AWS CloudTrail Security Best Practices to Keep in Mind Best practices for AWS CloudTrail security. When any kind of data is stored, security is almost always the hottest concern (as it should be.) By default, CloudTrail keeps log files encrypted using Amazon S3 Server Side Encryption (SSE). However, the bigger part of the responsibility falls on your shoulders, including:
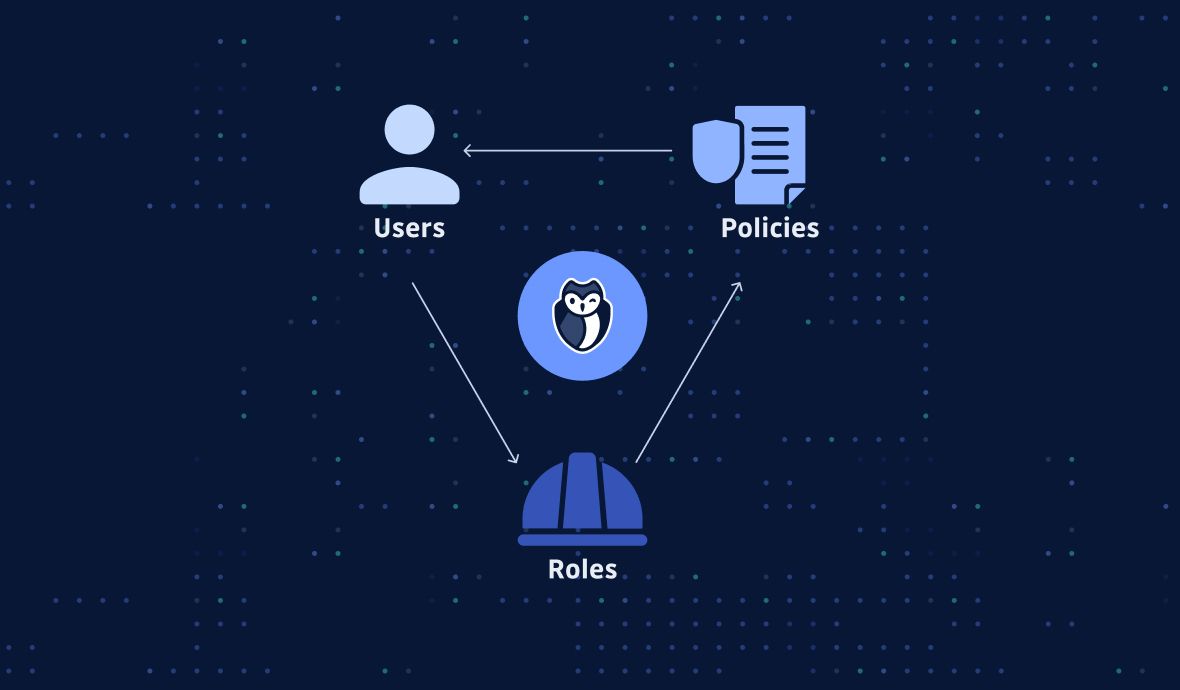
PDF AWS Security Best Practices resources. All charges for activities performed by your IAM users are billed to your AWS account. As a best practice, we recommend that you create an IAM user even for yourself and that you do not use your AWS account credentials for everyday access to AWS. See Security Best Practices in IAM for more information.
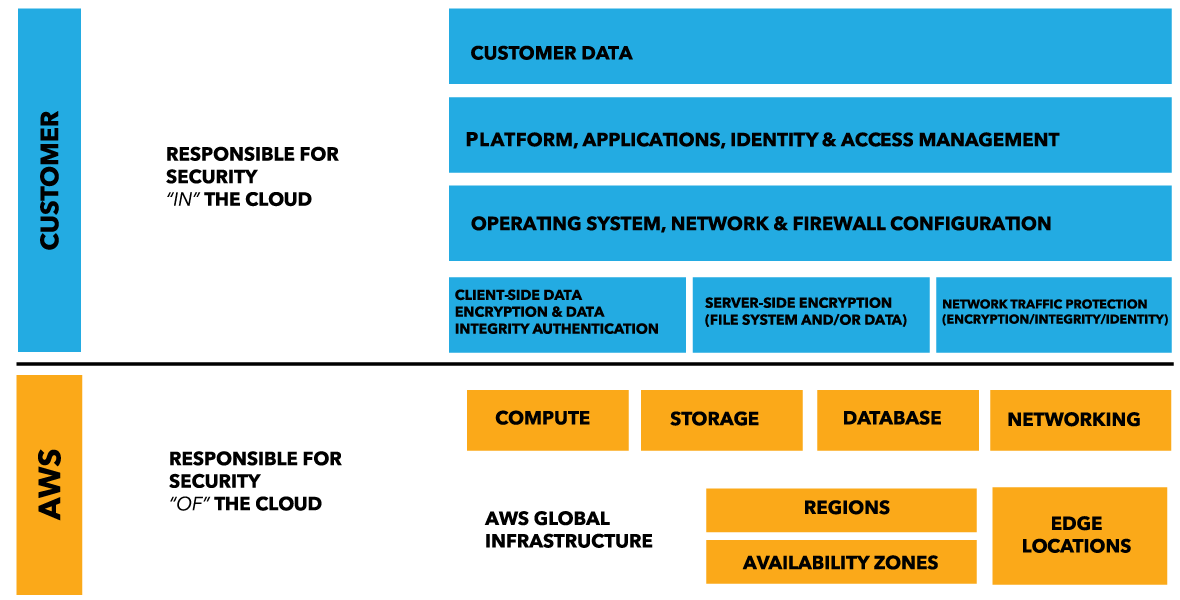
AWS VPC Security: 13 Best Practices [The 2022 Guide] - Hyperglance The best practice is to split your production, staging, and pre-production environments across different VPCs. Image courtesy of AWS 5. Use Security Groups To Control Resource Access It's vital that you factor in AWS Identity Access Management (IAM) when you're planning and setting up your VPC.
10 Best Practices for AWS Cost Optimization - Whizlabs Blog Also Check: Best AWS Cost Optimization Tips. Top 10 AWS Cost Optimization Best Practices. The scope for optimization of AWS costs is not limited to these three methods. So, you should try to explore other potential methods and tools that can support your AWS cost management. The following discussion presents the top ten recommended best ...
What are the Best AWS S3 Usage Best Practices? | nOps Here are some of the best AWS S3 usage best practices for optimal security and performance: Identify and Audit All Your AWS S3 Buckets. It's imperative to map out all S3 buckets to manage your S3 storage effectively. Identifying your crucial S3 buckets is an essential step towards security and stellar governance. nOps provides a 360-degree ...
13 AWS Security Best Practices - Check Point Software Achieving strong cybersecurity in the cloud can seem daunting, but it is not impossible. By following this AWS security best practices checklist, it is possible to improve the security of an AWS deployment. Identify Security Requirements. 1. Define and Categorize Assets in AWS: It is impossible to secure systems that you don't know exist.
Best practices for AWS Organizations - AWS Organizations Best practices for AWS Organizations - AWS Organizations AWS Documentation AWS Organizations User Guide Best practices for AWS Organizations PDF RSS We recommend that you follow these best practices when you create and operate your organization. Topics Best practices for the management account Best practices for member accounts
AWS Security Best Practices - AWS Security Best Practices AWS Security Best Practices. Notice: This whitepaper has been archived. For the latest technical information on Security and Compliance, see .
AWS Tags Best Practices and AWS Tagging Strategies AWS Tags Best Practices. While there isn't a perfect AWS tagging strategy that works for every organization, there are a few AWS tagging best practices that you should be familiar with. 1. Know how each AWS tag you create will be used. AWS cites four categories for cost allocation tags: technical, business, security, and automation. Consider which of these categories you will need when creating your AWS tagging strategy:
PDF Security Best Practices with Amazon ECR •ECR uses one AWS account for each stage: beta, gamma and prod •A micro-service has its own repoand deployment pipelinein each stage ... Best practices for ECR Image Scanning •Enable scan on push for each repository Turn on scan on push (it's free) for every repository. We're testing
AWS Fargate Security Best Practices - Alert Logic AWS Fargate Security Best Practices. AWS has become one of the most popular options for running containers because of its high reliability, strong security, and native integrations. There are multiple ways to containerize applications on AWS depending on your needs. AWS Fargate is a highly turnkey solution that offloads infrastructure ...
Establishing your best practice AWS environment Using a multi-account environment is an AWS best practice that offers several benefits: Rapid innovation with various requirements - You can allocate AWS accounts to different teams, projects, or products... Simplified billing - Using multiple AWS accounts simplifies how you allocate your AWS cost ...


















![AWS IAM: Best practices [Part 1] – DEVOPS DONE RIGHT](https://blog2opstree.files.wordpress.com/2021/03/image-36.png)









0 Response to "42 aws best practices"
Post a Comment